Ransomware – Protect your Business from a Growing Threat
Did you know that 90% of companies in the UK will experience some sort of downtime due to cyber attacks like ransomware? These attacks often result in significant loss of data, productivity, and revenue. Unfortunately, they are happening to all kinds of businesses each day.
Anyone who uses email and a connected device can be exposed to ransomware. However, businesses are especially vulnerable to this growing threat, as the data they hold can be extremely valuable, sometimes worth more than the profit they make through their day-to-day operations.
In this article, we’ll cover what businesses need to know about this type of malicious software, including how it works and how you can stop it from affecting your business.
What is ransomware?
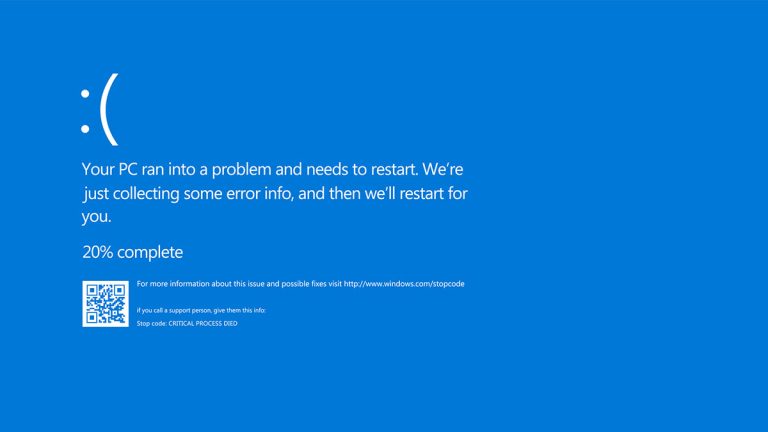
Ransomware is a class of malware (malicious software) that encrypts your files and prevents you from using them, locking you out of your device and data until you pay the cybercriminals who planted the software on your network.
Ransomware is a severe issue that can affect any business, large or small. It’s a frightening prospect to have all of your files and data held hostage until you pay the ransom.
How does ransomware work?
Step 1: Infection and distribution
Ransomware, like any malware, can gain access to an organisation’s systems in a number of different ways. These are known as ‘infection vectors’. Most ransomware variants have multiple infection vectors.
Many ransomware infections start with someone inside an organisation clicking on what looks like an innocent email attachment that, when opened, downloads the malicious payload and encrypts the network. This particular infection vector is more commonly known as a phishing email.
Phishing emails commonly exploit our fears and worries by using content related to current topics of concern like Covid, the cost of living crisis, or armed conflicts, for example. They use social engineering – manipulating our emotions – to stop us from being rational and start acting on impulse without thinking too much about what we’re actually doing.
Another common ransomware infection vector takes advantage of services like the Remote Desktop Protocol (RDP). An attacker who has stolen or guessed an employee’s login details uses them to access a computer within the enterprise network remotely. They can then download the malware and execute it on the machine under their control.
Step 2: Data encryption
Once the ransomware has gained access to a system, it can begin encrypting its files. Since encryption functionality is built into an operating system, this simply involves accessing files, encrypting them with an attacker-controlled key, and replacing the originals with the encrypted versions.
Most ransomware variants are intelligent enough not to encrypt files that ensure system stability. If they make the device completely unusable, it’s unlikely the ransom will be paid.
Step 3: Prevent recovery
Another common step of a ransomware attack is to prevent and disable the system restore features enabled by the operating system. Many ransomware variants will run commands to do one or more of the following tasks:
- Delete backups and shadow copies of files
- Wipe any free space
- Clear event logs
- Turn off services that aid in the recovery of a corrupted system
This step makes a recovery without the decryption key incredibly challenging.
Step 4: Ransom demand
At this stage, the ransomware prepares to make a ransom demand. Different ransomware variants implement this step in different ways, but most alter the desktop background to display a ransom note.
Others place a text file containing the ransom note in each encrypted directory. Typically, these notes demand a set amount of cryptocurrency in exchange for access to the victim’s files.
Step 5: Ransom payment
If the ransom is paid, the cybercriminal will either provide a copy of the private key used to protect the encryption key or a copy of the encryption key itself. This information can be entered into a decryptor program provided by the cybercriminal that can be used to reverse the encryption and restore access to the files.
However, even if you pay the ransom, there is no guarantee that you will get access to your computer or your files. Occasionally malware is presented as ransomware, but after the ransom is paid, the files are not decrypted. This is known as ‘wiper malware’.
It’s worth noting that if you do pay the ransom, you’re more likely to be targeted again in the future. So, malware prevention is always the best approach for your business.
Why is ransomware on the rise?
Ransomware made headlines throughout 2021 and continues to make the news throughout 2022. In fact, there has been a 52% increase in threats during the first half of the year than the same period in 2021.
You may have heard stories about attacks on large companies, organisations, or government agencies, or perhaps you, as an individual, have experienced a ransomware attack on your own device.
Medibank ransomware attack
One of the latest examples is a ransomware attack on Australian company Medibank, in which 200GB of data relating to 3.9 million customers was stolen. A large ransom was demanded (the exact amount has not been revealed).
The hacker used compromised, high-level credentials to steal records that included personal information like names, dates of birth, addresses, and gender identities, as well as Medicare numbers and health claims.
Ransomware for Christmas?
New ransomware groups are emerging all the time. Many of these attackers persist with the ‘big game hunting’ of large enterprises. However, SMBs are an increasingly popular target this year.
And, as Black Friday and Christmas approach, more of us are using websites to do business, look for bargains, and communicate. This is the perfect time of the year for ransomware attacks, especially phishing emails that promise special deals or discounts on high-demand products.
What are the risks of ransomware?
Disruption
A ransomware attack on your systems could paralyse your network. It could force you to close off parts of your business to ensure cybercriminals can no longer access your data.
In the time it takes you to investigate the cause of a breach and to get your systems back online, you will be unable to perform certain operations. You’re likely to experience a considerable loss of productivity as a result.
Lost revenue
Beyond the immediate impact that ransomware can have on your network, it can also result in an ongoing financial hit if you cannot provide your usual services to customers.
Market research1 has indicated that ransomware attacks cost UK businesses £346 million per annum.
Plus, the process of notifying customers of the security breach can be an expensive and time-consuming endeavour, meaning a further loss of revenue.
Damaged reputation
There is also the impact on your reputation to worry about too. In some industries, the fact that you’ve fallen victim to a cyberattack could potentially drive customers away permanently.
Financial penalties
If a password breach incident is severe enough, you will need to contact your data protection supervisory authority. In the UK, this is the ICO (Information Commissioner’s Office). You may incur financial penalties, depending on the data that was stolen.
Who is at risk from ransomware?
Ransomware attackers hit businesses, organisations, and individuals alike. Cybercriminals typically target specific tools and technologies, including:
- Mobile devices (using mobile malware)
- Remote desktop logins and tools
- Virtual Private Networks (VPNs)
- Public WiFi hotspots
- Cloud-based tools with poor password management
- Flaws in popular business software
- Website accounts with weak passwords
- Servers connected to the internet
How can you protect your business?
Many businesses and organisations in the UK are very much aware of the threat of malware. In fact, the average business now devotes more than a fifth of its IT budget to cybersecurity.
But the fact is, ransomware is constantly evolving to counter any efforts to thwart it, and businesses are now under siege from more attacks than ever before.
Training, education, and reporting
End-user or employee education must be central to any ransomware prevention effort. User education is one of the most important defences you can deploy, as the people in your business are often your first line of defence against attacks.
Cyber Awareness Training and Education helps people to identify an anomaly that could be part of a ransomware attack, including the tell-tale signs of a phishing email.
It’s critical that employees know exactly where to report anomalies and that they should do so with urgency. If employees are unable to recognise a security event or know how to report issues, the attack may continue
uninterrupted and continue to spread throughout the network.
MultiFactor Authentication (MFA)
As the name suggests, multifactor authentication (MFA) provides multiple layers of security and protection from attempts to access an account.
User accounts for cloud-hosted tools and file systems like Microsoft Teams, Google Drive or Dropbox should always be protected by 2-factor authentication. Enable MFA everywhere possible.
Anti-malware protection
The need to encrypt all of a user’s files means that ransomware has a unique fingerprint when running on a system. Anti-ransomware solutions are built to identify those fingerprints. Common characteristics of an effective anti-ransomware solution include the following:
- Wide variant detection
- Fast detection
- Automatic restoration
- Restoration mechanism not based on standard built-in tools
Patch management
A patch is a set of changes to a computer program, an app, or its supporting data designed to update, fix, or improve it. This includes fixing security vulnerabilities that criminals can exploit to infect a machine or entire networks.
Patching is critical in defending against ransomware attacks, as cyber-criminals will often look for the latest uncovered exploits in the patches made available and then target systems that are not yet patched.
As a business that relies on computer devices and networks, it’s critical you know when a patch becomes available so you can deploy it in a fast but controlled manner.
A Managed IT Support service will keep your systems and devices up-to-date, protected, patched, and secure, helping you avoid unplanned downtime, security breaches, and unexpected costs to fix issues and recover data.
There is a growing concern that cybercriminals can weaponise flaws in hardware and software faster than vendors can release patch updates or customers can patch them. So you really do need the most up-to-date and response patch management protection possible.
Vulnerability scanning
Vulnerability scanning can help businesses audit the safety of their existing systems and detect potential malicious code or files that have already been injected into systems. Once the code or files have been identified, they can be safely quarantined before a ransomware attack begins.
App and system updates
Protect mobile devices and laptops that are otherwise vulnerable if not updated with the latest security releases for their apps and operating systems by enabling automatic updates. In addition, centrally manage devices to only permit applications trusted by the business to run on company devices.
Filter and block incoming traffic
You can reduce the likelihood of malicious content reaching your devices through a combination of the following:
- filtering to only allow file types you would expect to receive
- blocking websites that are known to be malicious
- actively inspecting content
- using signatures to block known malicious code
- disabling RDP if it’s not needed
- using a Virtual Private Network (VPN)
These are typically done by network services rather than users’ devices.
Password and user authentication security
Passwords
Using only strong passwords is an essential part of protecting the security and identity of your business and its employees. Passwords are the weak point in systems and websites that cybercriminals actively target.
Poor password management, especially in these days of remote working, presents an additional risk factor – and attackers are taking full advantage.
User authentication security
As we talked about earlier, accessing services like RDP with stolen user credentials is a favourite technique of ransomware attackers. The use of strong user authentication can make it harder for an attacker to make use of a guessed or stolen password.
Backup and Recovery
Should the worst-case scenario happen, and your business is struck by a ransomware infection, you must get back up and running as quickly as possible. A disaster recovery plan allows you to document and execute a pre-planned list of actions to back up and restore your critical data without any data loss.
It’s essential to put your recovery plan to the test. Testing your disaster recovery process means undertaking a full system restore, including applications and operating systems, to ensure your backup and recovery process is viable.
Knowing your data is backed up and that those backups are good-to-go, ready for an emergency recovery to get you back up and running, will bring considerable peace of mind.
How can you mitigate a malware infection?
If your organisation has already been infected with malware, these steps may help limit the impact:
Disconnect
Immediately disconnect the infected computers, laptops or tablets from all network connections, whether wired, wireless or mobile phone-based.
Quarantine the machine(s)
Some ransomware variants will try to spread to connected drives and other machines. Limit the spread of the malware by removing access to other potential targets.
Leave the computer(s) on
The encryption of files may make a computer unstable. Powering off a computer can result in loss of volatile memory, so keep the computer on to maximise the probability of recovery.
Create a backup
Decryption of files for some ransomware variants is possible without paying the ransom. Make a copy of encrypted files on removable media in case a solution becomes available in the future or a failed decryption effort damages the files.
Check for decryptors
Check with the No More Ransom Project to see if a free decryptor is available. If so, run it on a copy of the encrypted data to see if it can restore the files.
Request help
An IT company or digital forensics expert may be able to recover copies of your data if they have not been deleted by the malware.
Wipe and restore
Restore the machine from a clean backup or operating system installation. This ensures that the malware is completely removed from the device.
Monitor
Monitor network traffic and run antivirus scans to identify if any infection remains.
Get the ransomware protection your business needs
To be fully confident that your business is protected from ransomware, you need to call the IT security protection experts from the RAD Group.
From our 24/7 IT management and support service to our data backup and recovery and enterprise-level security services, we have the solutions to protect your business against the cyber threats it faces today and in the future.
-
Underutilised Microsoft 365 apps and features
Underutilised Microsoft 365 apps and features The majority of UK businesses rely heavily on Microsoft 365. It's the productivity powerhouse... -
Hiring a technology consulting partner – best practices
Hiring a technology consulting partner – best practices If you’re considering partnering with an information technology company like us here... -
How to get ROI for your website
How to get ROI for your website In today's competitive online landscape, your website is your digital shopfront, brand ambassador,... -
Cybersecurity, cloud and automation – predicting IT budget spend in 2024
Cybersecurity, cloud and automation – predicting IT budget spend in 2024 As the UK business landscape continues to evolve, so... -
What is the true cost of IT downtime?
What is the true cost of IT downtime? In today's digital age, IT infrastructure is the backbone of any successful...